A look at DOS Malware ABR-1171.COM
In this post we will be looking at ABR-1171, which is infected by PS-MPC.c virus. This is a file infector type malware and is also know as Abraxas. File infectors are malware that scan the disk for all files and then overwrite them making them unusable. This particular malware infects only the first file present in the directory. This encrypted malware was first seen around 1993 and is of Russian origin. The group that wrote the malware is ARCV(Association of Really Cruel Viruses).
The virus detection rate is 40/56 on Virustotal.
Environment setup →
- Grab the latest version of DOSBox and install it. Link
- Grab the version of Debug build of DOSBox and place it in the installation folder. Link
Upon opening the file in a disassembler we can see that the first instruction is a jump to the unpacking routine. The unpacking routine can be replicated fairly easily since it’s a simple XOR. The IDApy script for unpacking is as follows.
from idautils import *
from idc import *
from idaapi import *
ea = 0x10100 # This is the start address of Seg000
end_ea = get_segm_end(ea)
patch_byte(ea,0x29)
patch_byte(ea+1,0xd8)
patch_byte(ea+2,0xc1)
for i in range(0,586,2):
patch_byte(ea+i,(get_wide_byte(ea+i) ^ 0xc1))
patch_byte(ea+i+1,(get_wide_byte(ea+i+1) ^ 0xd7))
plan_and_wait(ea,end_ea)
Now let’s look at what the malware does.
Function - Tone
This function is responsible for playing the tone. In the function we check if the speaker is on or not.
seg000:0129 in al, 61h
seg000:012B test al, 3
seg000:012D jnz plat_tone
seg000:012F or al, 3
seg000:0131 out 61h, al
Once this is done the malware sets the frequency of tones.
seg000:0144 int 1Ah
seg000:0146 add bx, dx
loop_back:
seg000:0148 int 1Ah
seg000:014A cmp dx, bx
seg000:014C jnz loop_back
The interrupt 1Ah with AH 0 returns the time, which is then compared until we hit the time set in the BX register. Once this is done we reset the speaker and return back.
Function - Find all files
This function is responsible for finding all the .exe files in a particular directory and overwriting with the malware file itself.
Function - Replace dosshell
This function is responsible for opening c:\\dos\\dosshell.com and copies the unpacked malware into it.
seg000:018B mov dx, 1B2h ; Name of file
seg000:018E xor cx, cx
seg000:0190 mov ax, 3C02h
seg000:0193 int 21h ; Open file
seg000:0195 xchg ax, bx
seg000:0196 mov ah, 40h ;
seg000:0198 mov cx, 493h ; len of bytes to write
seg000:019B mov dx, 100h ; OEP of malware
seg000:019E int 21h ; write to file
seg000:01A0 mov ah, 3Eh ; close file
seg000:01A2 int 21h
Function - Output to display
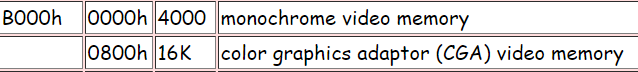
In this function it checks for the video modes. The check for the type of display is done using the interrupt 10, with AH set as 0fh. We see that a particular value is set depending on the value returned by the interrupt. A look at the video memory map of DOS tells us that value is the address of the video memory.
If the display type is mono then it prints out the string.
For he is not of this day...Nor he of this mind
If the display type is a 16bit color mode with res 720x400 it prints out

Putting it all together
After unpacking the malware, it turns the speaker on and plays a tone. The next few functions are responsible for overwriting the first file of the current directory and the previous directory. Then we have a function that replaces/overwrites the dosshell with a copy of the malware itself. On completion the malware prints out a graphic version of Abraxas as shown above. The malware does not reside in the memory.
References used:
http://www2.ift.ulaval.ca/~marchand/ift17583/dosints.pdf
https://www.osdata.com/system/physical/memmap.htm#MSDOS
https://www.csee.umbc.edu/courses/undergraduate/211/Spring00/Burt/lectures/CntlHardware/timer.html
http://cd.textfiles.com/thegreatunsorted/live_viruses/virus_collections/BBB/
